Amassing the Security:An Enhanced Authentication and Key Agreement Protocol for Remote Surgery in Healthcare Environment
Tsu-Yang Wu,Qian Meng,Lei Yang,Saru Kumari and Matin Pirouz
1Shandong University of Science and Technology,Qingdao,266400,China
2Chaudhary Charan Singh University,Meerut,Uttar Pradesh,250004,India
3California State University,Fresno,93740,USA
ABSTRACT The development of the Internet of Things has facilitated the rapid development of various industries.With the improvement in people’s living standards, people’s health requirements are steadily improving.However, owing to the scarcity of medical and health care resources in some areas,the demand for remote surgery has gradually increased.In this paper, we investigate remote surgery in the healthcare environment.Surgeons can operate robotic arms to perform remote surgery for patients,which substantially facilitates successful surgeries and saves lives.Recently, Kamil et al.proposed a secure protocol for surgery in the healthcare environment.However,after cryptanalyzing their protocol,we deduced that their protocols are vulnerable to temporary value disclosure and insider attacks.Therefore, we design an improved authentication and key agreement protocol for remote surgeries in the healthcare environment.Accordingly,we adopt the real or random(ROR)model and an automatic verification tool Proverif to verify the security of our protocol.Via security analysis and performance comparison,it is confirmed that our protocol is a relatively secure protocol.
KEYWORDS IoT;healthcare;security analysis;authentication;robotic arm;ROR
1 Introduction
As a novel paradigm, Internet of Things (IoT) [1–5] can effectively share data, coordinate and utilize resources.Simultaneously, in addition to reducing data transmission delay, the active of the emergence of the 5G[6]technology also improves the data transmission rate,which makes it possible to exchange of large amounts of data.This technology has been widely adopted in smart agriculture,smart cities, transportation, healthcare [7,8], artificial intelligence [9–11], etc., and has become an important part of people’s life.
Healthcare is an important application of the IoT.With the improvement of living standards,the requirements for medical and health care are gradually increasing.Today, there is a substantial demand for medical and health care systems.The application of IoT in healthcare involves the use of the most advanced internet technology to realize interactions between patients and doctors and medical institutions and medical equipment, which enables the informatization.With the help of IoT technology, artificial intelligence [12] and intelligent equipment, we can build a perfect IoT medical system to solve or reduce the problems of difficult medical treatment and tense doctor-patient relationships caused by the lack of medical resources.Although healthcare can provide people with significant convenience, several security problems [13–17] exist, such as the disclosure of patients’medical data and the tampering of patients’medical schemes by illegal personnel of the system.Many researchers have proposed a large number of schemes [12,18–20] to address the security problems inherent in the healthcare environment.However, some existing authentication and key agreement protocols have security vulnerabilities, such as against offline guessing, impersonation and insider attacks.Therefore,it is crucial to propose an AKA protocol to address these challenges.
Wu et al.[21]proposed an authentication scheme,suitable for telemedicine information systems(TMIS).However,Debiao et al.[22]have confirmed that their scheme is vulnerable to several security problems,such as impersonation attacks and insider attacks.To address these vulnerabilities,Debiao et al.[22]proposed an improved scheme,which is also applicable to TMIS.Wei et al.[23]proposed a protocol suitable for TMIS without the pre-deployment phase;however,Zhu et al.[24]verified that the protocol proposed by Wei et al.[23]could not resist offline password guessing attacks.Xu et al.[25] proposed an elliptic curve cryptography (ECC)-based scheme.They claimed that their protocol can effectively provide authentication and user anonymity.However, Islam et al.[26] pointed out that Xu et al.’s [25] scheme are vulnerable to replay attacks and smart card stolen attacks, incorrect password update phase, and failure to successfully complete mutual authentication.Subsequently,Islam et al.[26] proposed an improved protocol based on the that proposed by Xu et al.[25].The protocol was also designed based on ECC.Li et al.[27] designed an authentication scheme based on chaotic mapping;however,Madhusudhan et al.[28]proved that their scheme cannot successfully resist password guessing attacks.Zhang et al.[29]designed a three factor lightweight authentication agreement to address the problem of user anonymity in the e-healthcate system.However,Aghili et al.[30]pointed out that the agreement of Zhang et al.[29]cannot resist denial of service attacks(DOS)and insider attacks,as well as provide user untraceability and desynchronization.Therefore,Aghili et al.[30]proposed an improved scheme,which can provide user anonymity and mutual authentication.Sharma et al.[31] proposed a healthcare service authentication scheme based on cloud Internet of things, but Azrour et al.[32] pointed out that Sharma et al.’s [31] scheme could not resist user impersonatin attacks and offline password guessing attacks.Soni et al.[33]designed an authentication scheme for patient monitoring, but unfortunately, their scheme was proved by Xu et al.[34] that it could not provide perfect forward security.Kaur et al.[35] designed a secure protocol to solve the problem of security authentication in remote surgery.Ali et al.[36]designed a symmetric encryption and decryption scheme for TMIS; however, Yu et al.[37] discovered that this scheme [36] cannot withstand session key exposure attacks,man in the middle attacks(MITM)and impersonation attacks.Masud et al.[38] proposed a lightweight identity authentication scheme based on IoT healthcare.However,this scheme has been proved by Kwon et al.[39]that there are many security problems,such as offline password guessing,user impersonation,insider attacks and cannot ensure user anonymity.We summarize the literature reviewed in Table 1.
Influenced by COVID-19,the demand for remote surgery[40,41]under healthcare environment is gradually increasing.At the same time,the 5G network technology can transmit information with high efficiency and low delay,thereby facilitating remote surgery.The application of a remote surgery is shown in the Fig.1.Surgeons can operate robotic arms to perform remote surgery for patients,which enables a number patients infected with the virus to receive prompt treatment,reduces the spread of the virus,and provide the stable development of society.Although the development of this technology can bring several benefits,they are highly dependent on the network,and there will be some security problems.For example,if network delay occurs when a surgeon remotely manipulates a robotic arm to operate a patient, the surgeon cannot obtain feedback information in time, which will adversely affect the operation process and severely endanger the patient’s life.In addition,if an illegal surgeon manipulates the robotic arm or an unauthorized robotic arm is utilized, this will also threaten the safety of patients.Therefore,a secure lightweight authentication and key agreement protocol design is required to address these problems.
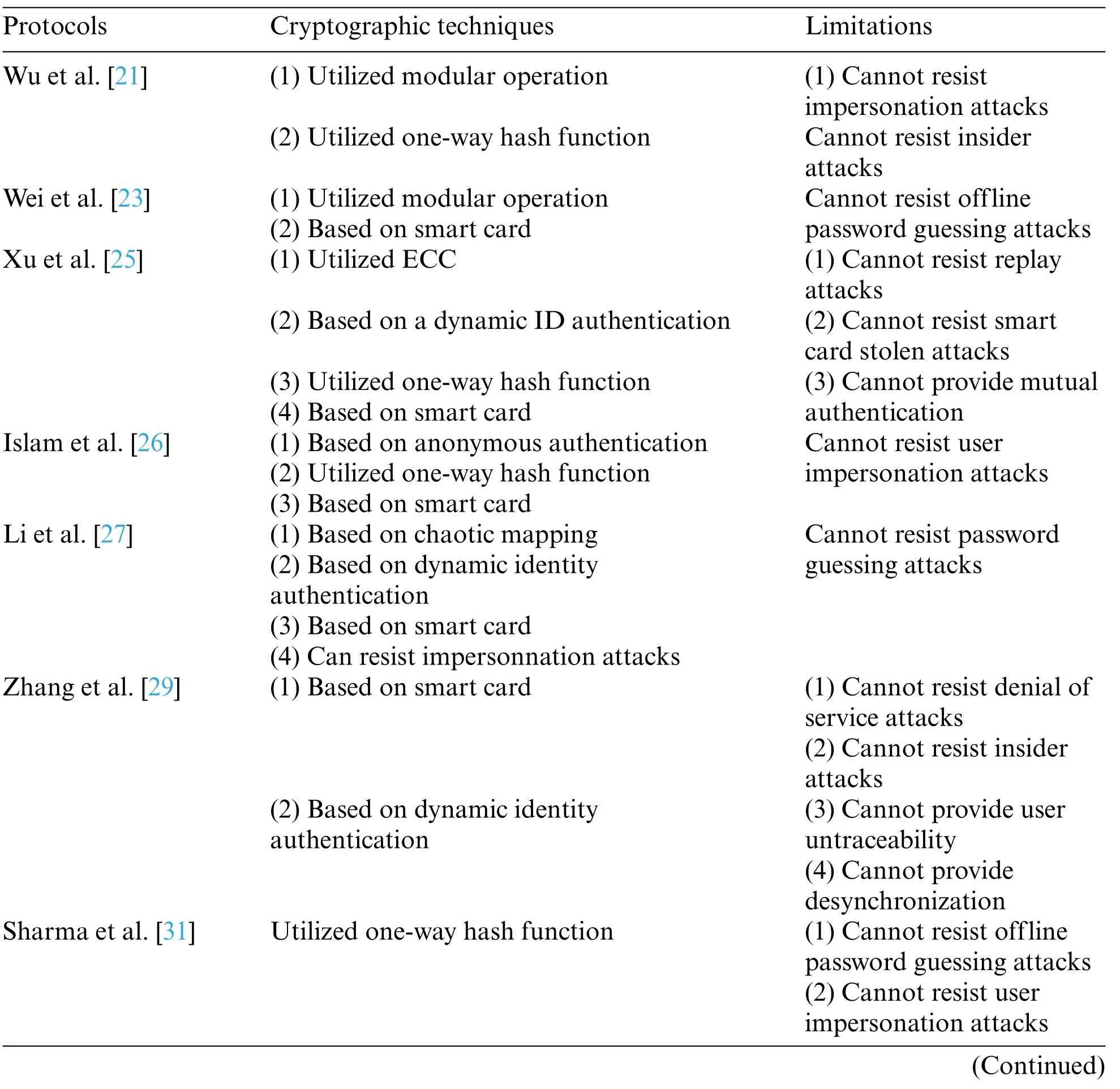
Table 1:Cryptographic techniques&limitations
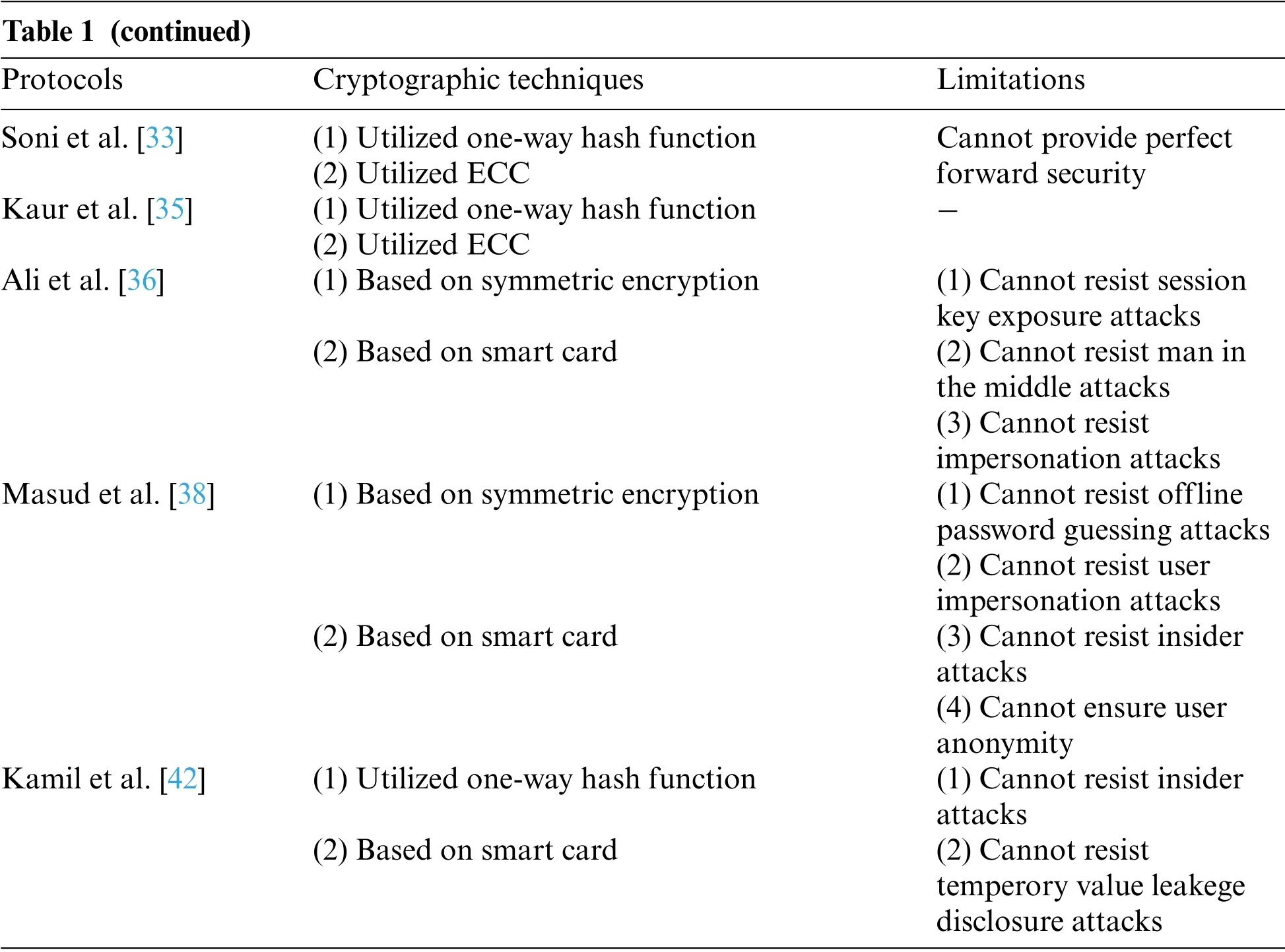
Table 1 (continued)Protocols Cryptographic techniques Limitations Soni et al.[33] (1)Utilized one-way hash function Cannot provide perfect forward security(2)Utilized ECC Kaur et al.[35] (1)Utilized one-way hash function -(2)Utilized ECC Ali et al.[36] (1)Based on symmetric encryption (1)Cannot resist session key exposure attacks(2)Based on smart card (2)Cannot resist man in the middle attacks(3)Cannot resist impersonation attacks Masud et al.[38] (1)Based on symmetric encryption (1)Cannot resist offline password guessing attacks(2)Cannot resist user impersonation attacks(2)Based on smart card (3)Cannot resist insider attacks(4)Cannot ensure user anonymity Kamil et al.[42] (1)Utilized one-way hash function (1)Cannot resist insider attacks(2)Based on smart card (2)Cannot resist temperory value leakege disclosure attacks
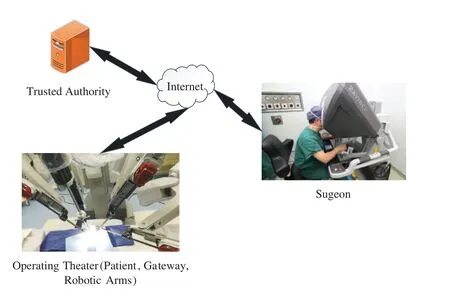
Figure 1:The application of a remote surgery
Recently, Kamil et al.[42] designed a lightweight authentication protocol that primarily solves identity authentication problem in remote surgery.Its remote surgery framework is illustrated in Fig.2.This framework comprises four entities:a trusted authority(TA),surgeon,gateway,and robotic arm.All medical data during surgery is transmitted through tactile networks.To protect the security and privacy of medical data, the entire operation process needs to be completed under the detection ofTA.Before surgery, surgeons and gateways, and the robotic arm must register withTAand obtain a legal identity.After each entity completes its registration, the surgeon, gateway, and robotic arm jointly decide on a session key to transmit data during surgery.They claim that their protocol is secure and efficient.However,we find that their protocol is vulnerable to temporary value disclosure attacks and insider attacks.In this paper,we propose an enhanced protocol suitable for this environment.Our contributions are:(1)We point out that Kamil et al.’s protocol has some security problems.(2)To solve these security problems,we propose an enhanced authentication protocol for remote surgery.Unlike Kamil et al.’s protocol,the registration phase of the robotic arm does not register with theTAvia the gateway,because in an operating machine,the gateway and robotic arm are in the same system.We use ProVerif tool and ROR model to evaluate the security of the protocol.In addition,we use informal analysis to conduct a detailed security evaluation of the protocol,and prove that the protocol can resist common attacks,such as MIMT,replay attacks,impersonation attacks,insider attacks,etc.(3)Finally,through security and performance comparison,we find that our protocol is secure and suitable for the remote surgery environment.
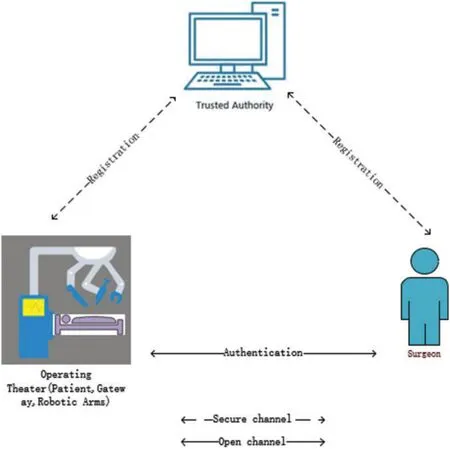
Figure 2:Network model
The remainder of this paper are arranged as follows.In Section 2,we review the protocol proposed by Kamil et al.The cryptanalysis of their protocol is then comprehensively introduced in detail in Section 3.In Section 4,we introduce our proposed protocol.Then,Section 5 presents a few security analyses of our protocol, while the performance comparison is introduced in Section 6.Finally,Section 7 concludes this paper.
2 Review of Kamil el at.Protocol
In this section, we review the protocol presented by Kamil et al.[42].This protocol comprises seven phases;however,in this paper,we only adopt four phases:surgeon registration phase,gateway and robotic arm registration phase,user login,authentication and key agreement phase.
2.1 Surgeon Registration Phase
Surgeons are required to register with theTAas legitimate users to utilize robotic arms for remote surgeries.Messages at this stage are transmitted on a secure channel.The detailed steps are presented as follows in Table 2:
(1)SiselectsIDi,PWi,and a random numberbi,computesDi=h(IDi‖bi),HPWi=h(PWi‖bi),and then sends{Di,HPWi}toTA.
(2) After receiving the message sent bySi,TAselects a random numberci,computesα=h(ci‖Dk)⊕h(Di‖HPWi),andβ=ci⊕h(IDk‖Dk),stores{α,β,h(·)}in the smart card(SC),and then sendsSCto the user.
(3) After receivingSC,SicomputesA1=h(PWi‖IDi)⊕bi,A2=h(bi‖HPWi‖Di),and stores the{A1,A2}in theSC.
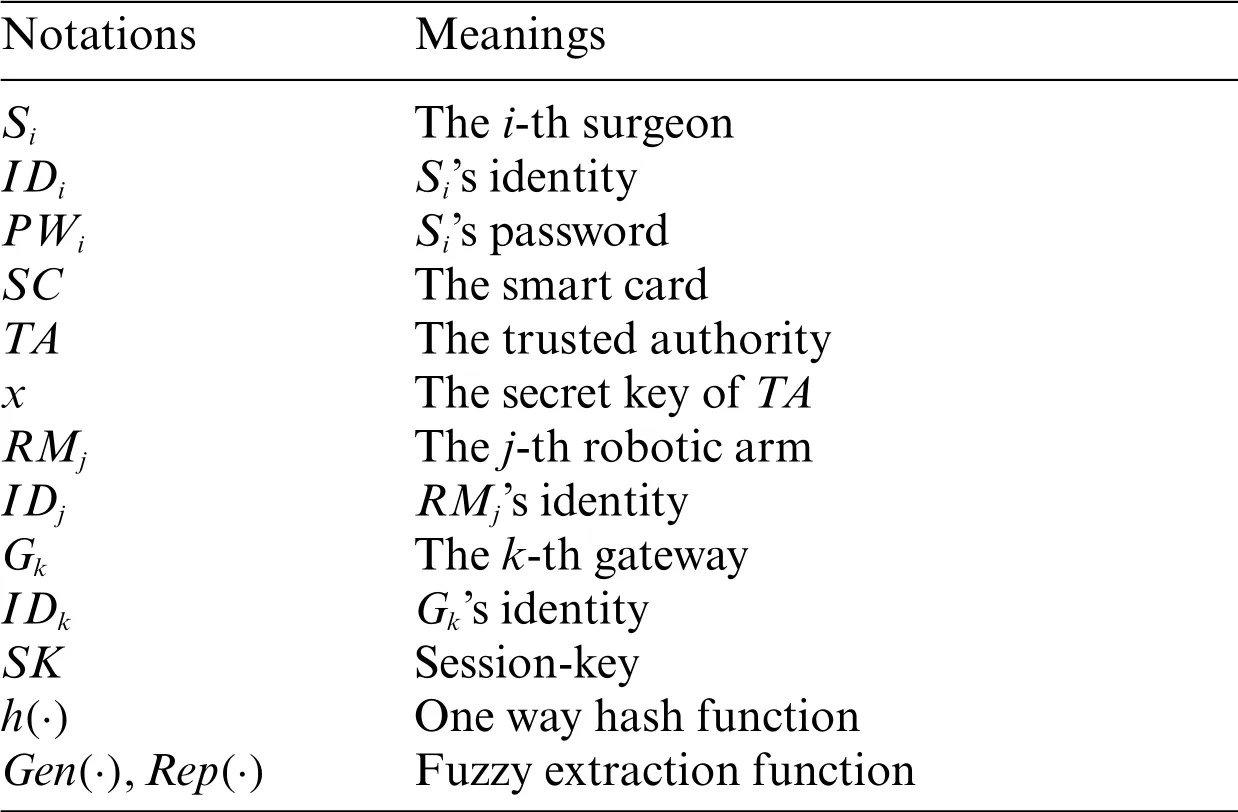
Table 2:Notations and their meanings
2.2 Gateway and Robotic Arm Registration Phase
At this phase,TAselects their respective identities forGkandSNj, computes some private parameters,and then transmits these private parameters toGkandSNjthrough secure channels.The detailed steps are presented as follows:
(1)TAselects its own identityIDTA,a hash functionh(·),andIDj,IDk,respectively,for the identity ofGkandSNj,selects a random numbers,computesDk=h(s‖IDTA‖IDk),Dj=h(s‖IDTA‖IDj),and sends{IDk,Dk,IDj,Dj}to the gateway.
2) After receiving the message sent byTA,Gkstores {IDk,Dk,IDj,Dj} in its own memory, and then sends{IDj,Dj}toRMj.
3)RMjreceives the message sent byGkand stores{IDj,Dj}in its own memory.
2.3 Login and Authentication Phase
1)SiinputsIDi,PWi,computesbi=A1⊕h(PWi‖IDi),Di=h(IDi‖bi),HPWi=h(PWi‖bi),A*2=h(bi‖HPWi‖Di), and then performs authentication by checking.If the authentication is successful,Siselects a random numberr1and timestampT1, and then computesA3=α⊕h(Di‖HPWi),A4=β⊕T1,A5=h(r1‖A3‖T1),andA6=(r1‖A5)⊕A3.After completing computation, it transfers the messageM1= {A4,A5,A6,T1} through the common channel toGk.
2) After receiving the messageM1sent bySi,Gkfirst computesc*i=A4⊕h(IDk‖Dk)⊕T1,A*3=h(c*i‖Dk),andr*1‖A5=A6⊕A3,and then verifies the timestamp|Tk-T1|andA*5A5,whereA5=h(r1‖A*3‖T1).If both are verified,Gkwill select a random numberr2and timestampT2,computesA7=ci⊕h(IDj‖Dj‖r2‖r*1‖T2),A8=Dj⊕(r2‖r*1‖T2),A9=h(IDj‖Dj‖‖r2‖T2),and then send the messageM2= {A7,A8,A9}toRMjthrough the commonchannel.
3) After receiving messageM2,RMjfirst computesr2‖r1‖T2=A8⊕Djand then verifies the timestamp|TR-T2|.If the validation is successful,RMjcomputesc*i*=A7⊕h(IDj‖Dj‖r*2‖r*1*‖T2),A*9=h(IDj‖Dj‖c*i*‖r*2‖T2)and checksA*9A9to verify the identity ofGk.Subsequently,if the identification is successful,RMjselects a random numberr2and timestampT3,computesK1=h(r*2‖r*1*‖r3),A10=h(r*2‖r3‖K1‖IDj‖Dj‖T3),A11=(r*3‖T3)⊕r2,and then sends messageM3={A10,A11}toGkthrough the common channel.
4) After receiving the messageM3,Gkcomputesr*3‖T3=A11⊕r2and verifies the timestamp|Tk-T3|.If the verification is successful,Gkcomputes the session keyK2=h(r2‖r*1‖r3),then computesA*10=h(r2‖r3‖K2‖IDj‖Dj‖T3),and verifies the correctness of the session key throughA*10=?A10.After the successful verification,Gkselects the timestampT4,computesA12=h(K2‖r2‖r*3‖A9‖T4),A13=(r2‖r*3‖T4)⊕r*1, and then transmits the messageM4={A8,A12,A13}toSithrough the common channel.
5) After receiving the messageM4,Siobtains the value ofr*2‖r*3*‖T4by computingA13⊕r1,and then verifies the timestamp|TS-T4|ΔT.If the verification is successful,Sicomputes the session keyK3=h(r*2‖r*3*‖r1),A*12=h(K3‖r*2‖r*3*‖A9‖T4), and verifies whether the session key is correct by checking
3 Cryptanalysis of Kamil et al.’s Protocol
In this section,based on the following attacker model[43],we analyze the security of the protocol proposed by Kamil et al.[42], and subsequently deduce that this protocol cannot resist temporary value disclosure attacks,insider attacks.
Attacker Model:Based on D-Y model[44],we define attackerAhas the following capabilities:
1)Acan block, steal, change and replay messages transmitted via a common channel, but a cannot obtain information transmitted via a secure channel;
2)Acan steal the surgeon’s smart card and extract the information stored in the smart card through power analysis;
3)Acan be a malicious entity and can obtain the information stored in the gateway.Acan also obtain the information stored in robotic arm’s memory.
3.1 Insider Attacks
Insider attacks refers to a malicious person in the system who obtains the information stored in the system by other entities,uses the messages on the public channel,and finally successfully calculates the session key.Suppose a malicious attackAin the hospital obtains the content{IDk,Dk,IDj,Dj}stored in the gateway during the registration phase,then he can launch the following attacks.
3.1.1 Impersonate the Surgeon
1)Aobtains the message {IDj,Dj} stored in the gateway, and messagesM1= {A4,A5,A6,T1}andM2= {A7,A8,A9} on the common channel are also intercepted.Then,Acan calculater2‖r1‖T2=A8⊕Dj,ci=A7⊕h(IDj‖Dj‖r2‖r*1‖T2),β=A4⊕T1,andA3=(r1‖A5)⊕A6.
2)Areselects a random numberr′1and timestampT1′,then calculatesA′4=β⊕T1′,A′5=h(r′1‖A3‖T1′),A′6=(r′1‖A′5)⊕A3,and then sends messageM1′={A′4,A′5,A′6,T1′}toGk.
3) After receiving messageM1′,Gkcalculatesc′i=A′4⊕h(IDk‖Dk) ⊕T1′,A′3=h(c′i‖Dk),r′1‖A′5=A′6⊕A′3.Subsequently,Gkchecks the timestamp|Tk-T1′|,if true,GkverifieswhereA*5=h(r1‖A*3‖T1).If the verification is successful,Gkselectesr2,T2,computesA7=c′i⊕h(IDj‖Dj‖r2‖r′1‖T2),A8=Dj⊕(r2‖r′1‖T2),A9=h(IDj‖Dj‖c′i‖r2‖T2),and then sends the messageM2={A7,A8,A9}toSNj.
4) AfterSNjreceivesM2,it calculatesr2‖r′1‖T2=A8⊕Dj,and then checks|TR-T2|.If true,SNjverifiesA*9A9,wherec′i=A7⊕h(IDj‖Dj‖r2‖r′1‖T2),A*9=h(IDj‖Dj‖c′i‖r2‖T2).If the verification is successful,SNjselectsT3,r2,K1=h(r2‖r′1‖r3),A10=h(r2‖r3‖K1‖IDj‖Dj‖T3),A11=(r3‖T3)⊕r2.Then it sends messageM3={A10,A11}toGk.
5) After receivingM3,Gkcalculatesr*3‖T3=A11⊕r2and checks|Tk-T3|;if true,it calculatesK2=h(r2‖r′1‖r3).GkverifiesA*10A10, whereA*10=h(r2‖r3‖K2‖IDj‖Dj‖T3).If the verification is successful,GkselectsT4, calculatesA12=h(K2‖r2‖r*3‖A9‖T4),A13=(r2‖r*3‖T4)⊕r′1,and then sendsM4={A8,A12,A13}toSi.
6) At this point,Aintercepts the messageM4sent byGkand calculatesr*2‖r*3‖T4=A13⊕r′1,and the final session keyK=h(r*2‖r*3‖r′1).
3.1.2 Derive Session key
1.Aintercepts the messageM2={A7,A8,A9}transmitted on the common channel.Accordingly,Acan calculater2‖r1‖T2=A8⊕Dj.
2.Afterr2andr1are calculated,Aintercepts the messageM3= {A10,A11} transmitted on the common channel,and then calculatesr*3‖T3=A11⊕r2.Therefore,Acan calculate the session keyK2=h(r2‖r*1‖r3).
In summary, we logically infer that the protocol proposed by Kamil et al.[42] cannot resist privileged insider attacks.
3.2 Temperory Value Disclosure Attacks
Assuming that attackerAobtains the random numberr1selected by surgeonSkin the login authentication phase, and intercepts the messageA13transmitted on the public channel, he can obtain the values ofr*2andr*3*by computingA13⊕r1, andAcan easily calculate the session keyK=h(r*2‖r**3‖r1).Therefore, it can be concluded that their proposed protocol cannot resist the temporary value disclosure attacks.
4 The Proposed Protocol
In this section,we introduce the proposed protocol.The protocol comprises four phases:surgeon registration phase,gateway registration phase,robotic arm registration phase,login and authentication phase.Each phase will be comprehensively described in detail next.
4.1 Registration Phases
The registration phase mainly includes gateway registration,surgeon registration and robtic arm registration,which will be described in detail.
Surgeon Registration Phase:Before operating with a robotic arm,a surgeon must register with theTAas a legal user via a secure channel.Fig.3 shows the surgeon’s registration process.The specific steps necessary for this registration are as follows:
1) The surgeonSiselects his ownIDi,PWi,BIOi,and a random numberai,and then computesGen(BIOi)=(σi,τi),RPWi=h(PWi‖ai),Ai=h(IDi‖RPWi‖σi),TRPWi=h(RPWi‖σi).Subsequently,TAsends{IDi,TRPWi}toTA.
2) After receiving the information sent bySi,TAselects a random numberbi,and then computesX=x⊕h(bi‖TRPWi),Bi=h(IDi‖x)⊕TRPWi,Di=bi⊕TRPWi.Subsequently,TAissues a smart cardSCto theSi,stores{Bi,Di}into theSC,and sends it toSi.
3) After receiving theSCsent byTA,the surgeon stores{Ai,τi}in theSC.
Gateway Registration Phase:Before being utilized,the gateway must register with theTAand generate some private data for the authentication phase.Fig.4 shows gateway’s registration process.The specific steps required are as follows:
1.The gateway selects its ownIDkand sends it to theTA.
2.After receiving the message sent by the gateway,TAselects a random numberdk, computesGk=h(IDk‖dk),Gx=Gk⊕x,and then sendsGk,dkto the gateway.
3.Subsequently,the gateway storesGk,dkin its own memory.
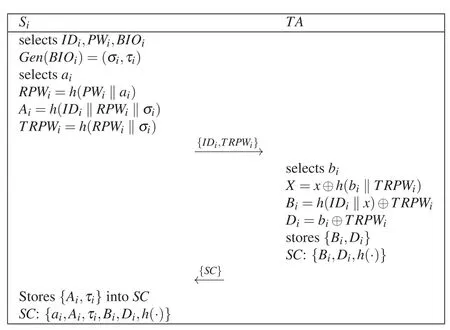
Figure 3:Surgeon registration
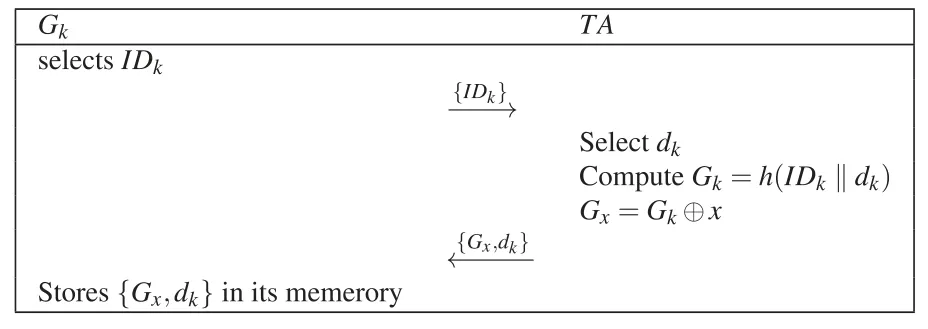
Figure 4:Gateway registration phase
Robotic Arm Registration Phase:Because the robotic arm and gateway are in the same system,the robotic arm is solely required to register with the gateway via a secure channel.Fig.5 shows robotic arm’s registration process.The specific steps required are comprehensively presented as follows:
1) The robotic armRMjselects its identityIDjand sends it to the gateway via a secure channel.
2) After receiving a message sent by the robotic arm, gateway selects a random numbercj, and computesx=h(IDk‖dk)⊕Gx,Ej=h(IDj‖x),Fj=cj⊕Ej;subsequently,GkstoresFjand then sends{Ej,Fj}toRMj.
3) FinallyRMjsaves{Ej,Fj}in its memory.
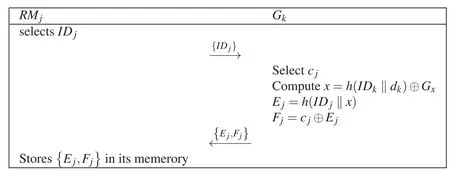
Figure 5:Robotic arm registration phase
4.2 Login and Authentication Phase
Before performing long-distance operations, surgeons need to manipulate robotic arms via an access gateway.AfterSilogs into the system,Gkfirst verifiesSi’s identity, and then sends an authentication request toRMj.AfterRMjcompletes the authentication,Gksends an authentication message toSi.After mutual authentication, the three entities establish a common session key for communications.The specific login authentication and session key establishment process are shown in Table 3 and comprehensively described as follows:
1)SiinputesIDi,PWi,inprintsBIOi,and computesσi′=Rep(BIOi,τi),RPWi=h(PWi‖ai),=h(IDi‖RPWi‖σi′),Ai′=h(IDi‖RPWi‖σi′),by checkingAi′Aito verify whether the legality ofSi’s identity.If the verification process is successful,Siselects a random numberr1and timestampT1, computesTRPWi′=h(RPWi‖σi′),h(IDi‖x)=Bi⊕TRPWi′,bi=Di⊕TRPWi′,x=X⊕h(bi‖TRPWi),C1=IDi⊕h(IDk‖x),C2=SIDj⊕h(h(IDi‖x)‖bi),C3=r1⊕h(bi‖IDi),C4=h(r1‖IDi‖IDj‖bi‖T1), and sends the messageM1={Di,Bi,C1,C2,C3,C4,T1}toGk.
2) After receiving the messageM1sent bySi,Gkfirst checks the timestamp|T1-Tk|ΔT.If the verification is successful,it computesx=h(IDk‖dk)⊕Gx,IDi=C1⊕h(IDk‖x),TRPWi=Bi⊕h(IDi‖x),bi=Di⊕TRPWi,SIDj=C2⊕h(h(IDi‖x)‖bi),r1=C3⊕h(bi‖IDi),=h(r1‖IDi‖IDj‖bi‖T1), and checksC4′C4to verifySi.If the verification passes,Gkselects the timestampT2and random numberr1,computesEj=h(IDj‖x),cj=Fj⊕Ej,PIDj=h(IDj‖cj),C5=r2⊕PIDj,C6=h(PIDj‖r2‖cj‖T2),C7=r1⊕h(r2‖cj),C8=h(bi‖cj)⊕h(IDj‖r2),and then sends the messageM2={C5,C6,C7,C8,T2}toSNj.
3) After receiving the messageM2sent byGk,SNjfirst checks the timestamp|T2-Tj|.If the verification is successful,SNjcomputescj=Fj⊕Ej,PIDj=h(IDj‖cj),r2=C5⊕PIDj,C6′=h(PIDj‖r2‖cj‖T2),C′6?=C6;if trueGkselectsr3,T3,and verifiesGk’s identity by computingIf this verification is successful,SNjselects a random numberr3and timestampT3,computesr1=C7⊕h(r2‖cj),h(bi‖cj)=C8⊕h(IDj‖r2),SK=h(r1‖r2‖r3‖h(bi‖cj),C9=h(SK‖h(bi‖cj) ‖T3),C10=r3⊕h(r1‖IDj),and then sends the messageM3= {C9,C10,T3}to the gateway.
4) After receiving the messageM3fromSNj,Gkfirst checks the timestamp |T3-Tk|and computesr3=C10⊕h(r1‖IDj),SK=h(r1‖r2‖r3‖h(bi‖cj),C′9=h(SK‖h(bi‖cj) ‖T3);subsequently,Gkverifies the identity ofSNjby calculatingC′9C9.After successful verification,GkselectsT4,computesC11=r2⊕h(TRPWi‖r1),C12=h(bi‖cj)⊕h(bi‖IDi),=h(SK‖r2‖r3‖T4),and sends messageM4toSi.
5) WhenSireceives the message fromGk, it first validates the timestamp |T4-Ti|ΔT, then computesr3=C10⊕h(r1‖IDj),r2=C11⊕h(TRPWi‖r1),h(bi‖cj) =C12⊕h(bi‖IDi),SK=h(r1‖r2‖r3‖h(bi‖cj)),=h(SK‖r2‖r3‖T4),and finally verifiesC13′C13.If the verification is successful,SisavesSKfor future communication.
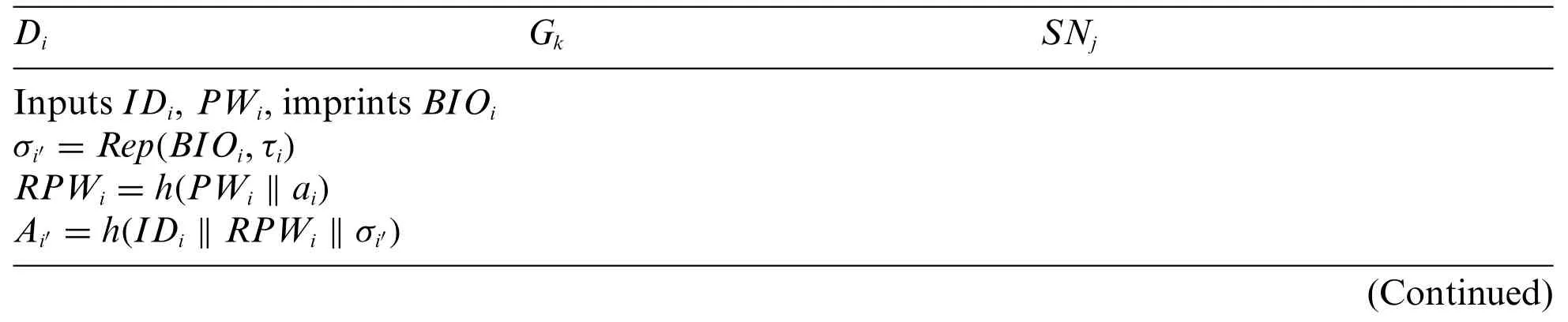
Table 3:Login and authentication phase
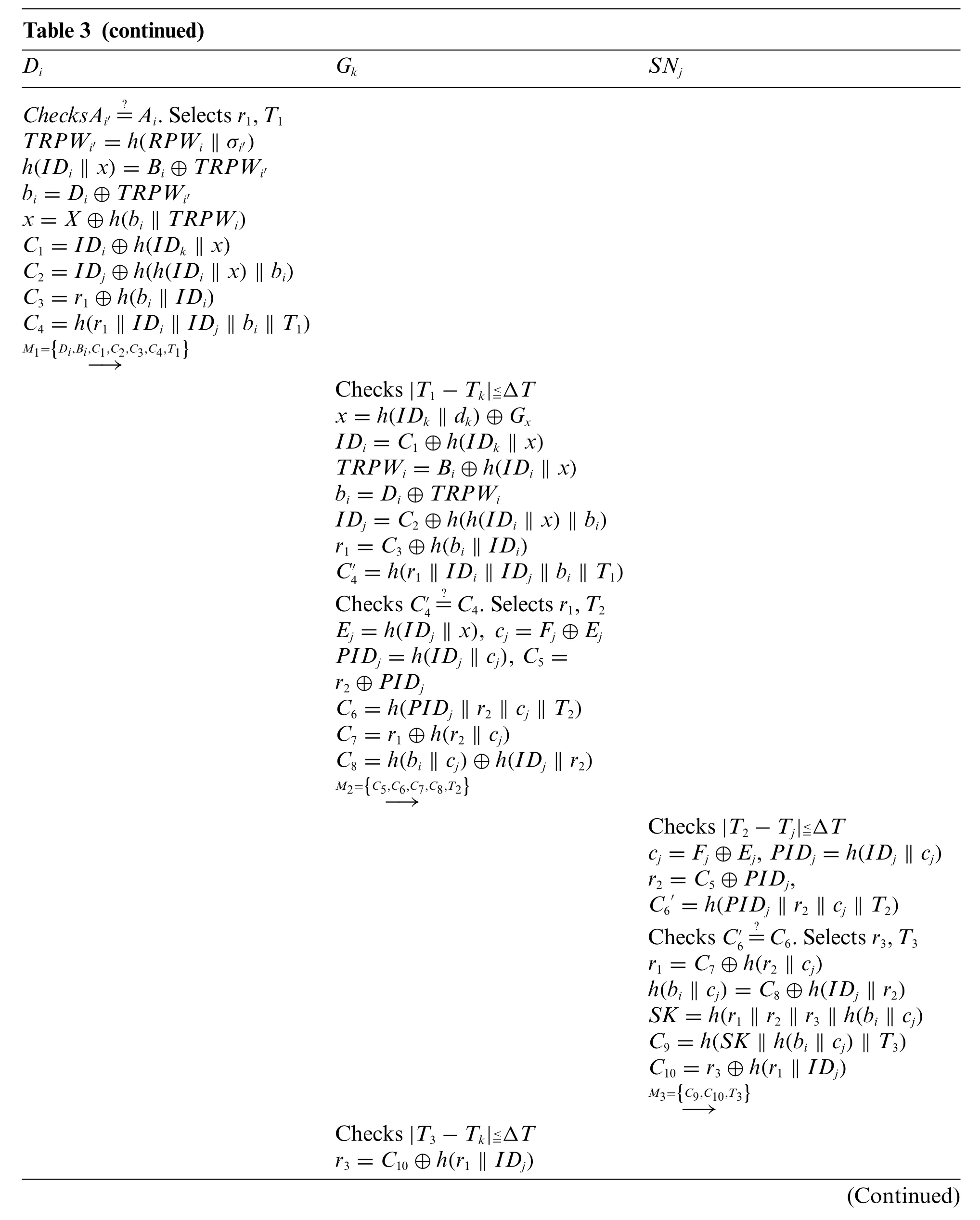
Table 3 (continued)Di Gk SNj?=Ai.Selects r1,T1 TRPWi′ =h(RPWi ‖σi′)h(IDi ‖x)=Bi ⊕TRPWi′bi =Di ⊕TRPWi′x=X ⊕h(bi ‖TRPWi)C1 =IDi ⊕h(IDk ‖x)C2 =IDj ⊕h(h(IDi ‖x)‖bi)C3 =r1 ⊕h(bi ‖IDi)C4 =h(r1 ‖IDi ‖IDj ‖bi ‖T1)ChecksAi′M1={Di,Bi,C1,C2,C3,C4,T1}-→Checks|T1-Tk|images/BZ_323_1937_1381_1957_1420.pngΔT x=h(IDk ‖dk)⊕Gx IDi =C1 ⊕h(IDk ‖x)TRPWi =Bi ⊕h(IDi ‖x)bi =Di ⊕TRPWi IDj =C2 ⊕h(h(IDi ‖x)‖bi)r1 =C3 ⊕h(bi ‖IDi)C′4=h(r1 ‖IDi ‖IDj ‖bi ‖T1)Checks C′4?=C4.Selects r1,T2 Ej =h(IDj ‖x), cj =Fj ⊕Ej PIDj =h(IDj ‖cj), C5 =r2 ⊕PIDj C6 =h(PIDj ‖r2 ‖cj ‖T2)C7 =r1 ⊕h(r2 ‖cj)C8 =h(bi ‖cj)⊕h(IDj ‖r2)M2={C5,C6,C7,C8,T2}-→Checks|T2-Tj|images/BZ_323_1937_1381_1957_1420.pngΔT cj =Fj ⊕Ej, PIDj =h(IDj ‖cj)r2 =C5 ⊕PIDj,C6′=h(PIDj ‖r2 ‖cj ‖T2)Checks C′6?=C6.Selects r3,T3 r1 =C7 ⊕h(r2 ‖cj)h(bi ‖cj)=C8 ⊕h(IDj ‖r2)SK =h(r1 ‖r2 ‖r3 ‖h(bi ‖cj)C9 =h(SK ‖h(bi ‖cj)‖T3)C10 =r3 ⊕h(r1 ‖IDj)M3={C9,C10,T3}-→Checks|T3-Tk|images/BZ_323_1937_1381_1957_1420.pngΔT r3 =C10 ⊕h(r1 ‖IDj)(Continued)
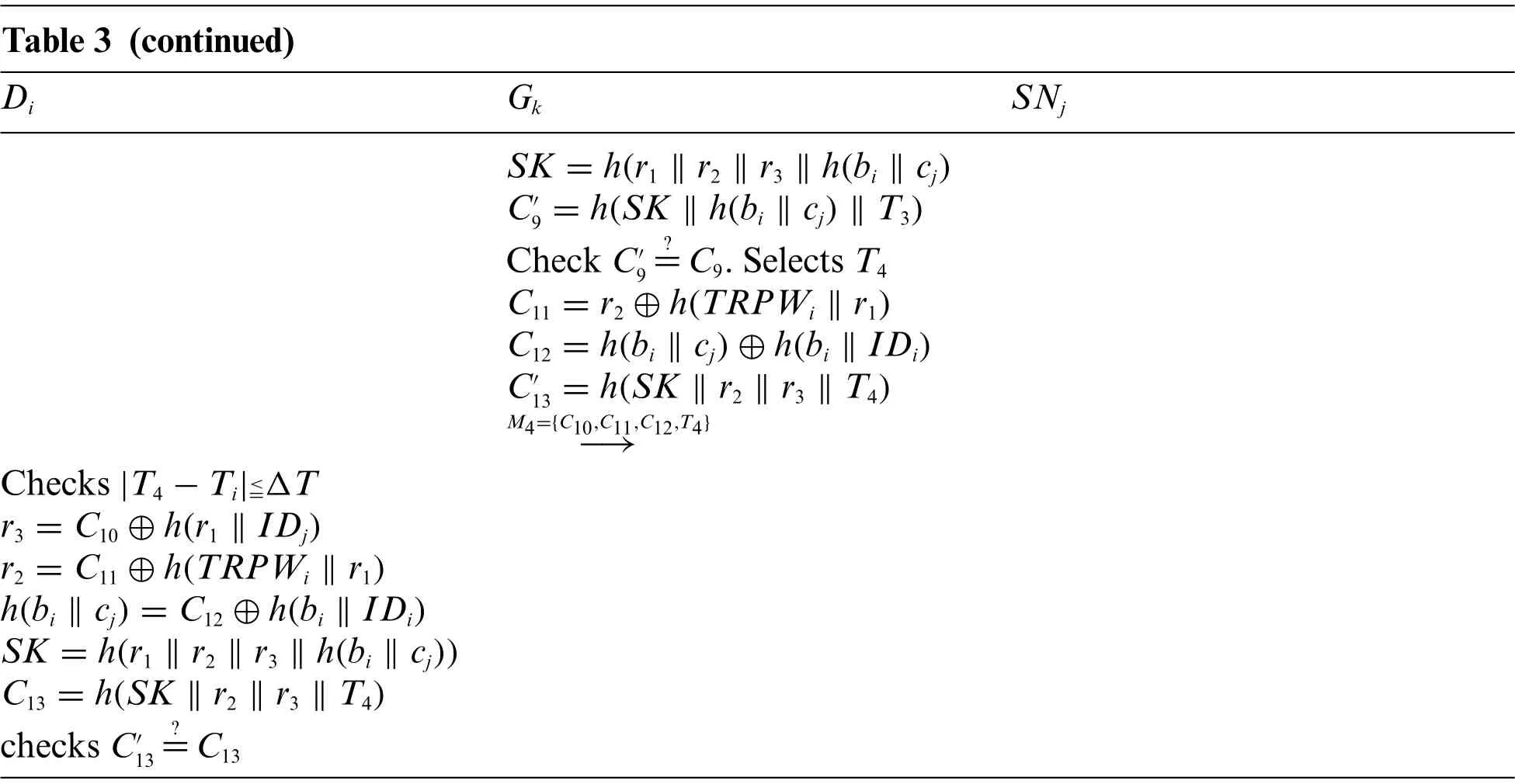
Table 3 (continued)Di Gk SNj SK =h(r1 ‖r2 ‖r3 ‖h(bi ‖cj)C′9=h(SK ‖h(bi ‖cj)‖T3)Check C′9?=C9.Selects T4 C11 =r2 ⊕h(TRPWi ‖r1)C12 =h(bi ‖cj)⊕h(bi ‖IDi)C′1 3 =h(SK ‖r2 ‖r3 ‖T4)M4={C10,C11,C12,T4}-→Checks|T4-Ti|images/BZ_323_1937_1381_1957_1420.pngΔT r3 =C10 ⊕h(r1 ‖IDj)r2 =C11 ⊕h(TRPWi ‖r1)h(bi ‖cj)=C12 ⊕h(bi ‖IDi)SK =h(r1 ‖r2 ‖r3 ‖h(bi ‖cj))C13 =h(SK ‖r2 ‖r3 ‖T4)checks C′13?=C13
5 Security Analysis
In this section,we adopt Proverif,ROR model,and informal analysis to validate the security of our proposed protocol
5.1 Proverif
Four entities are adopted in our protocol:TA,Gk,SiandRMj.According to the registration and authentication processes of the four entities in the protocol,we utilize Proverif[45,46]to describe the entire protocol process,which is comprehensively presented below:
1)chandschare used to represent common channel and secure channel, respectively.The registration phase is carried out on the secure channel,while the login and authentication phase is conducted on the public channel.The session key adoptsSKi,SKj, andSKkto represent the session key of the surgeon, robotic arm, and gateway, respectively.We also define some operations,such ashash,XOR,etc.The defined query is adopted for security verification.The specific function definition is presented in Figs.6a–6c.
2)Si’s process is illustrated in Fig.7a.
3)Gk’s process is presented in Fig.7b.
4)Rj’s process is illustrated in Fig.7c.
5)TA’s process is shown in Fig.7d.
6) Fig.6d presents the obtained verification results.The final results are “Query not attacker(SKi[]) is true,”“Query not attacker (SKj[]) is true,”“Query not attacker (SKk[]),”“Query inj-event(SurgeonAuthed)==>inj-event(SurgeonStarted)is true,”“Query inj-event(RMAcGateway) ==>inj-event(GatewayAcSurgeon) is true,” “Query inj-event(GatewayAcRM)==>inj-event(RMAcGateway)is true,”and“Query inj-event(SurgeonAcGateway)==>injevent(GatewayAcRM) is true.” Therefore, our protocol can successfully pass the security verification of Proverif and resist attacks.
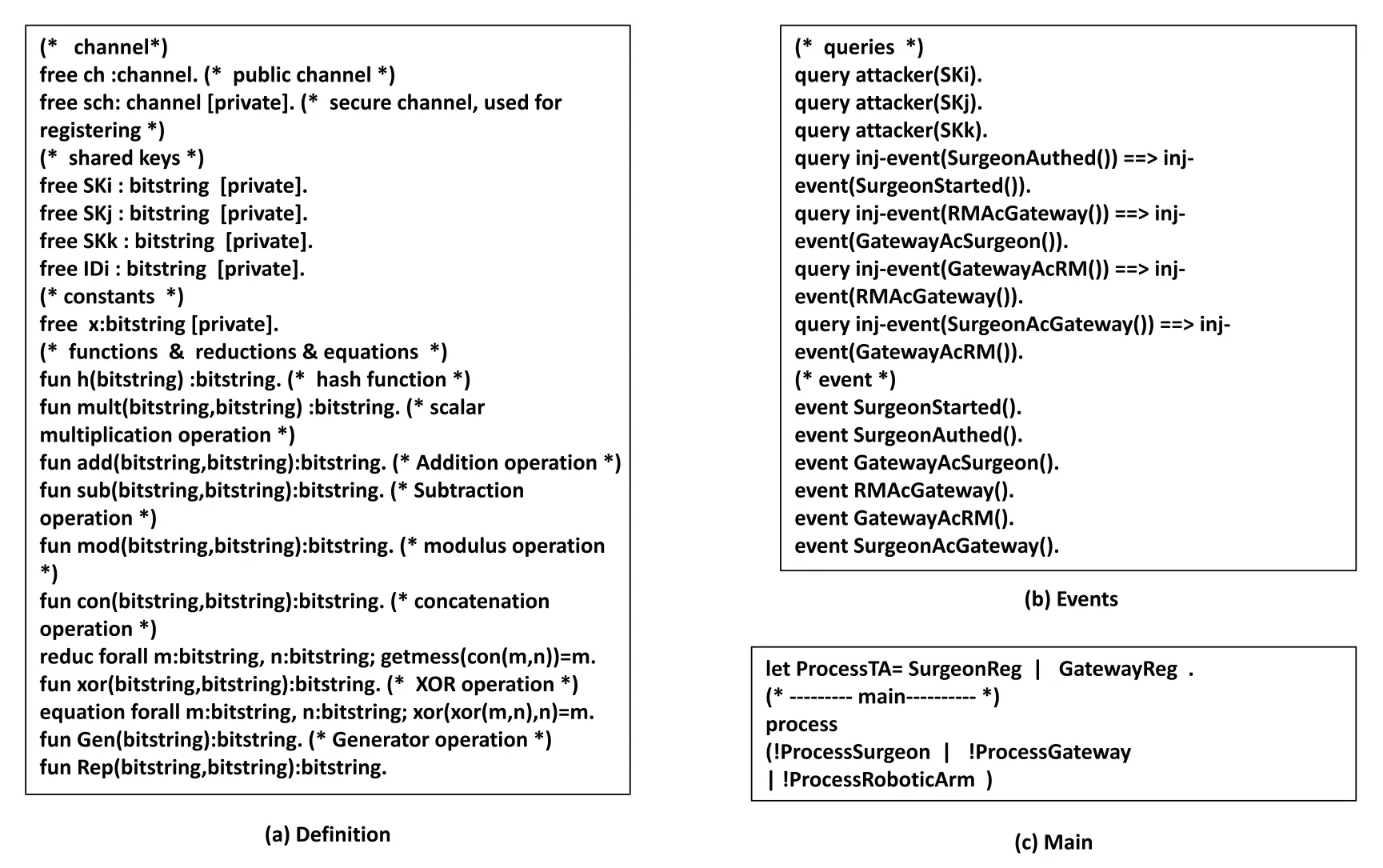
Figure 6:Definitions and results
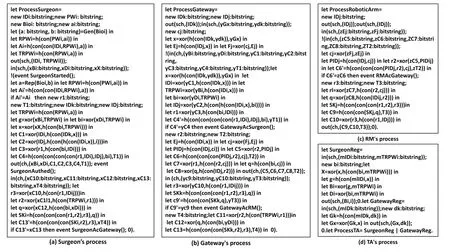
Figure 7:Process
5.2 Formal Security Analysis
In this section,we perform a security analysis on the proposed protocol in the ROR[19,47]model to demonstrate the protocol’s security.
5.2.1 ROR Model
The proposed protocol contains four entities:a surgeon, gateway,TA, and robotic arm.In the ROR model,we adoptto denote thex-th doctor’s instance,y-th robot arm instance,z-th gateway, and then-thTA, respectively.We assume that attackerAcan possess the following query capabilities:
Execute(Y):If the attacker executes this query,it intercepts the messages transmitted betweenSi,GkandSNjon the public channel.The specific query is shown in Table 4.
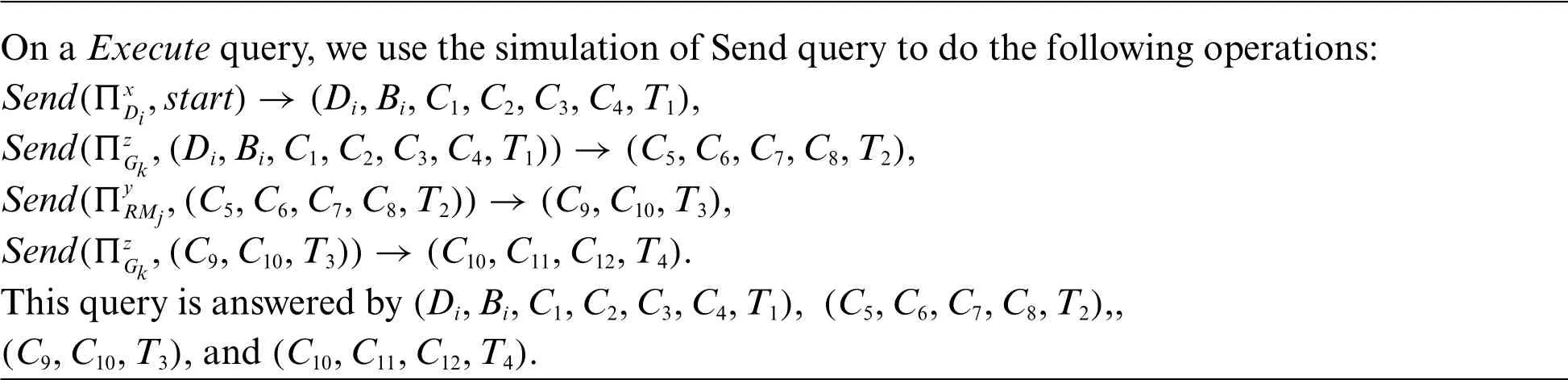
Table 4:Simulation of Execute
Send(Y,M):If the attacker executes this query,it sends the messageMtoY,and can receive a response fromY.The specific query is shown in Table 5.
Hash(string):If an attacker executes this query, it enters a string and gets its hash value.The specific query is shown in Table 6.
Corrupt(Y):If an attacker executes this query,it obtains the private value of an entity,such as a long-term private key,a parameter stored inSC,or a temporary message.The specific query is shown in Table 6.
Test(Y):If the attacker executes this query,it flips a coinc.Ifc= 1,Aobtains the correctSK,and ifc=0,Aobtains a string with an equal length to theSK.The specific query is shown in Table 6.
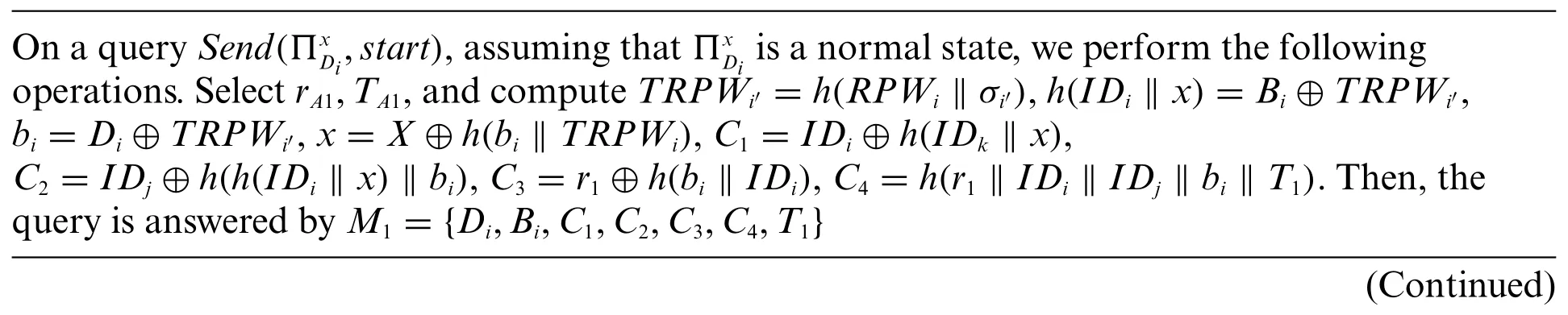
Table 5:Simulation of Send query
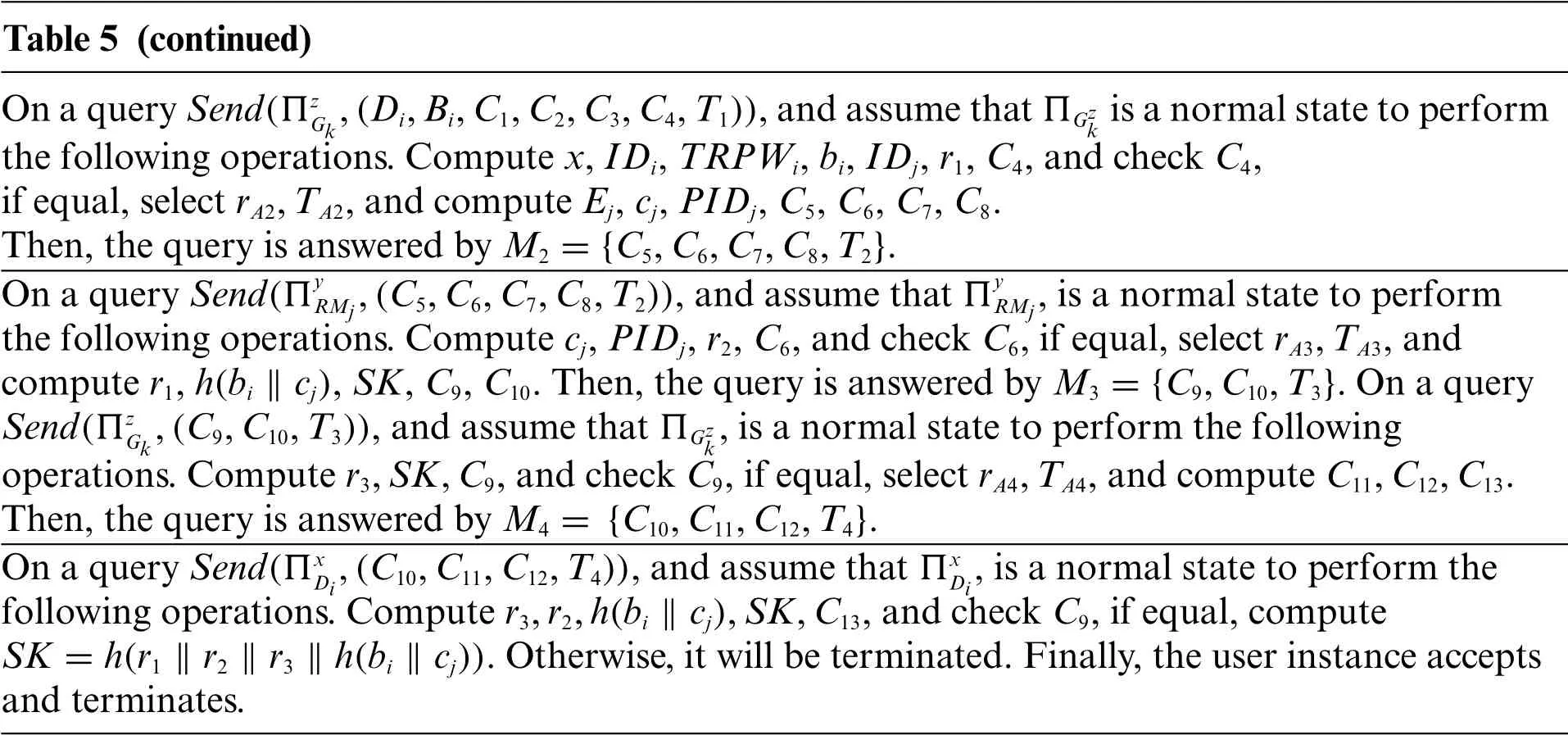
Table 5 (continued)On a query Send(ΠzGk,(Di,Bi,C1,C2,C3,C4,T1)),and assume that ΠGzk is a normal state to perform the following operations.Compute x,IDi,TRPWi,bi,IDj,r1,C4,and check C4,if equal,select rA2,TA2,and compute Ej,cj,PIDj,C5,C6,C7,C8.Then,the query is answered by M2 ={C5,C6,C7,C8,T2}.On a query Send(ΠyRMj,(C5,C6,C7,C8,T2)),and assume that Πy RMj,is a normal state to perform the following operations.Compute cj,PIDj,r2,C6,and check C6,if equal,select rA3,TA3,and compute r1,h(bi ‖cj),SK,C9,C10.Then,the query is answered by M3 ={C9,C10,T3}.On a query Send(ΠzGk,(C9,C10,T3)),and assume that ΠGzk,is a normal state to perform the following operations.Compute r3,SK,C9,and check C9,if equal,select rA4,TA4,and compute C11,C12,C13.Then,the query is answered by M4 = {C10,C11,C12,T4}.On a query Send(Πx Di,(C10,C11,C12,T4)),and assume that ΠxDi,is a normal state to perform the following operations.Compute r3,r2,h(bi ‖cj),SK,C13,and check C9,if equal,compute SK =h(r1 ‖r2 ‖r3 ‖h(bi ‖cj)).Otherwise,it will be terminated.Finally,the user instance accepts and terminates.
5.2.2 Theorem
In the ROR model, ifAcan execute the queriesExecute(Y),Send(Y,M),Hash(string),Corrupt(Y),andTest(Y),then the probability that the attacker can break the proposed protocolPin polynomial time is:Here,qsenddenotes the number of queries executed;qhashrefers to the number ofHashexecutions;C’ands’are two constants,andlrepresents the bit length of the biological information[48].
5.2.3 Proof
We played five rounds of the game,GMi(i=0,1,2,3,4).is denoted as the probability thatAcan win inGMi.The detailed simulation steps of the query in the game are presented below.
GM0:This game commences by flipping a coinc.GM0does not perform query; hence, we can obtain the probability thatAcan successfully breakPas follows:

GM1:GM1is an execute query added toGM0.A can only intercept messagesM1,M2,M3,M4transmitted on the common channel inGM1.Subsequently,Awill obtainSKbyTest(Y)query;however,r1,r2,r3cannot be obtained.Hence,the probability ofGM1is equal to that ofGM0.

GM2:GM2is based onGM1with the addition of Send query,and according to Zipf’s law[48],we can obtain the probability ofGM2as follows:

GM3:GM3is based onGM2with theHashquery added and theSendquery removed.According to the birthday paradox,we can get the probability ofGM3as:

GM4:InGM4,we analyze two events to verify the security ofSK=h(r1‖r2‖r3‖h(bi‖cj)).One is to verify perfect forward security by obtaining the long-term keyxofTA,and the other is to obtain temporary information to verify that the protocol can resist temporary information disclosure attacks.
1) Perfect forward security:AadoptsΠTAnto obtain the long-term keyxofTA,ororto obtain the private value of the registration phase.
2) Temporary information disclosure attack:Aadoptsto obtain the temporary information of the three parties.
For the first event,even ifAgets the long-term keyxofTA,or the private values of both in the registration phase,the random numbersr1,r2andr3cannot be computed;hence,Acannot compute the value ofSK,whereSK=h(r1‖r2‖r3‖h(bi‖cj)).For the second event,even ifAcan obtainr1,the values ofr2,r3,bi,andcjare kept secret;hence,SKcannot be computed.Similarly,even ifAcan obtainr2orr3, the value ofSKcannot be computed.Accordingly, we can obtain the probability ofGM4as:
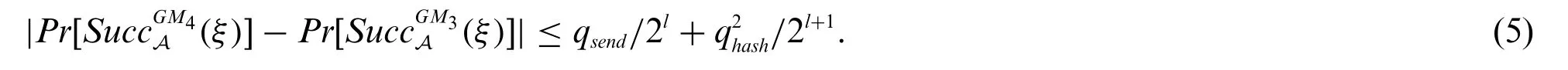
GM5:InGM5,AadoptsCorrupt(A)to query the smart card for parameters{ai,Ai,τi,Bi,Di,h(·)}and we show that that the proposed protocol is resistant to offline key guessing attacks.Siis registered using the passwordPWiand biometricBioi.Aattempts to guessAi=h(IDi‖RPWi‖σi′);however,IDi,RPWiandσiare kept secret.The probability thatAguesses bits of biological information is:1/2l[49].In Zipf’s law[48],whenqsend≦106,the probability thatAcan guess the password is greater than 0.5.Therefore,we can obtain the probability ofGM5as:
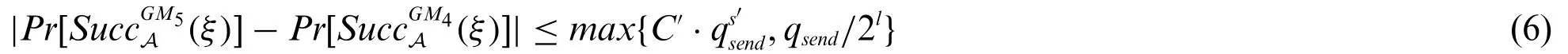
GM6:InGM6,to verify whether the protocolPcan resist the impersonate attack,Aqueriesh(r1‖r2‖r3‖h(bi‖cj)),and the game is terminated.Hence,we can obtain the probability ofGM6as:

Because the probabilities of the success and failure ofGM6are equal,the probability thatAcan guess the session key is:

According to the above formula,we can obtain
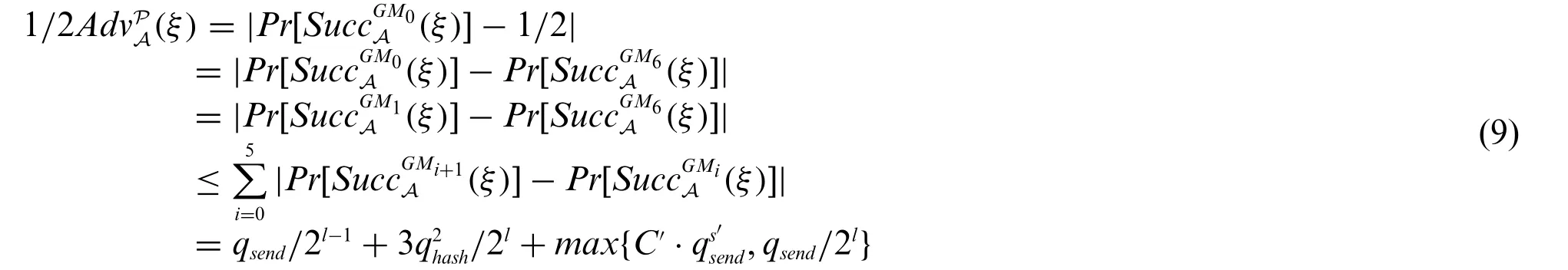
Therefore,we can obtain
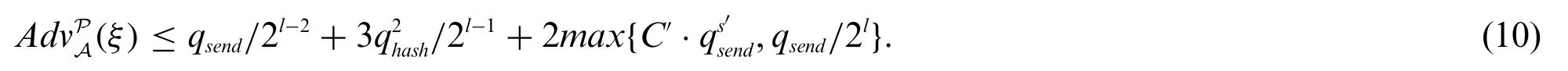
It is not difficult to infer that our protocol has successfully passed the security verification of ROR model, and that it can resist offline password guessing attacks, smart card stolen attacks, random number disclosure attacks,as well as provide perfect forward security.
5.3 Informal Security Analysis
In this section,we verify that our proposed protocol can resist some common attacks.
5.3.1 Impersonation Attacks
AttackerAis likely to impersonate any one of the surgeon,gateway,and sensor nodes.
1) Impersonate Surgeon:An attackerAcan attempt to impersonate a surgeon by intercepting a messageM1= {Di,Bi,C1,C2,C3,C4,T1}on the public channel.He attempts to computeC1=IDi⊕h(IDk‖x),C2=IDj⊕h(h(IDi‖x)‖bi),andC3=r1⊕h(bi‖IDi);however,Adoes not know the values ofx,bi,andIDi, Consequently he cannot compute the values ofC1,C2,C3,andC4accurately.So he cannot calculate to re-initiate a new messageM′1.Therefore,attackerAcannot impersonate a legitimate surgeon.
2) Impersonate gateway:An attackerAintercepts the messageM2={C5,C6,C7,C8,T2}transmitted on the common channel,tries to computePIDj=h(IDj‖cj),C6=h(PIDj‖r2‖cj‖T2),C7=r1⊕h(r2‖cj),C8=h(bi‖cj)⊕h(IDj‖r2), and change some of its values.However,becauseAcannot obtain the value ofcj, he cannot computePIDjandr2, and thus cannot correctly compute the value ofC6,therefore,they cannot re-initiate a messageM2′,as well as impersonate a legitimate gateway.
3) Impersonate robotic arm:When an attackerAwants to impersonate a legitimate robotic arm,he does so by intercepting the messageM3={C9,C10,T3}on the common channel and tries to computeC9,whereC9=h(SK‖h(bi‖cj) ‖T3)is the value for which gateway authenticates theRMj,but he cannot compute to get the values ofr1,r2andh(bi‖cj),soSK=h(r1‖r2‖r3‖h(bi‖cj))andC9cannot be computed.Therefore,attackerAcannot re-initiate a message,so he cannot successfully impersonate a legitimate robotic arm.
Therefore,we can conclude that our protocol can successfully resist impersonation Attacks.
5.3.2 Man-in-the-Middle AttacksIf an attackerAwants to launch a man-in-the-middle attack,he can do so by intercepting messageM1= {Di,Bi,C1,C2,C3,C4,T1}on the common channel and trying to turnM1intoM1′by changing the value ofr1orT1.ButAdoes not know the values of messages {IDi,TRPWi,Di}, so he cannot computebi=Di⊕TRPWi,x=h(IDk‖dk)⊕Gx,C2=IDj⊕h(h(IDi‖x)‖bi),C3=r1⊕h(bi‖IDi),andC4=h(r1‖IDi‖IDj‖bi‖T1).In this case,Aalso cannot compute and changeM2,M3andM4,so our protocol can resist the man-in-the-middle attacks.
5.3.3 User Anonymity
Since no information aboutSi’s identity is directly stored inSi’s smart card, an attacker cannot obtainSi’s identity information through smart card stolen attacks.Moreover,althoughAcan intercept the messageM1={Di,Bi,C1,C2,C3,C4,T1}on the public channel,Adoes not know the values ofxandIDk;hence the attacker cannot obtain theIDiofSiby computingIDi=C1⊕h(IDk‖x).Therefore,our protocol can provide user anonymity.
5.3.4 Insider Attacks
We assume that attackerAobtains the information {Gx,dk,Fj} stored by the gateway in the registration phase,but sinceAdoes not knowx,he cannot computecj=Fj⊕Ej,PIDj=h(IDj‖cj),and the values ofr1,r2,r3are also unknown toA,soAcannot compute the session keySK=h(r1‖r2‖r3‖h(bi‖cj).Therefore,our protocol is resistant to insider attacks.
6 Security and Performance Comparison
In this section, we compare the security and performance with the protocols of Sharma et al.[31],Soni et al.[33],Kaur et al.[35],Masud et al.[38]and Kamil et al.[42],which are applicable to the healthcare environment.The detailed results of the comparison are comprehensively described in subsections.
6.1 Security Comparison
In this subsection,we compare the security of these five protocols.√and×are used to indicate whether certain safety characteristics are satisfied.Implies that this characteristic is not considered.The comparison results are shown in Table 7.As can be seen from the table,Sharma et al.[31]protocol cannot resist user impersonation attacks and offline password guessing attacks.The protocol of Soni et al.[33]cannot provide perfect forward security.The protocol proposed by Masud et al.[38]cannot resist user impersonation attacks, offline password guessing attacks and insider attacks, and cannot provide user anonymity.The protocol of Kamil et al.[42]cannot resist insider attacks and temporary value disclosure attacks.The protocol in[35]and our protocol are secure.
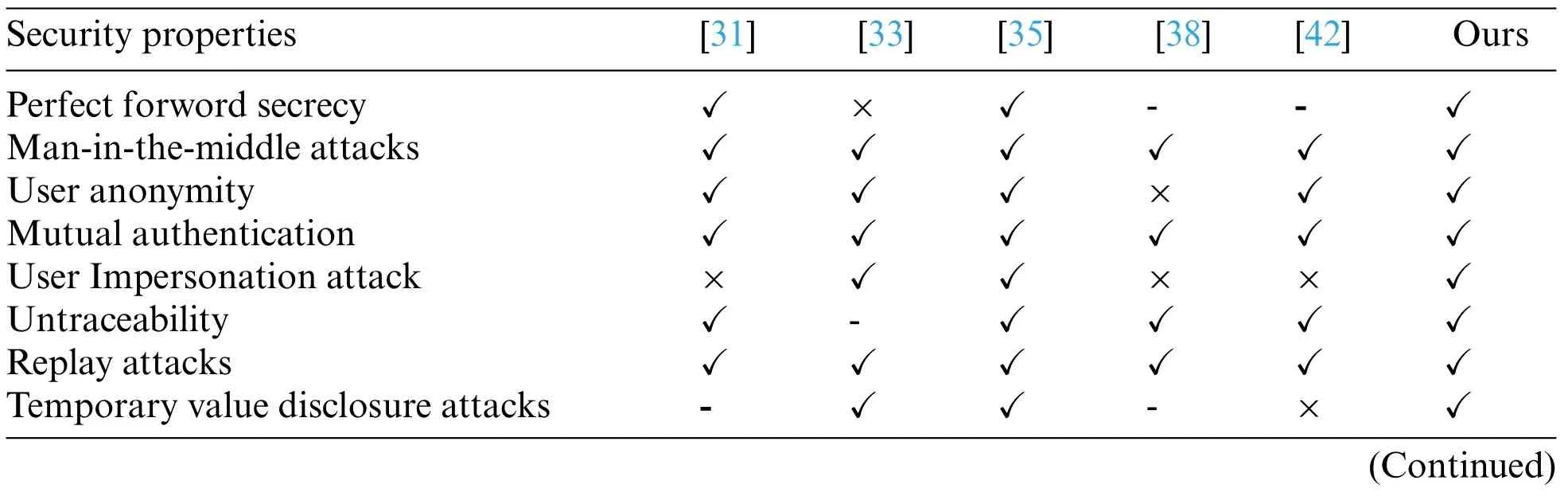
Table 7:Comparisons of security
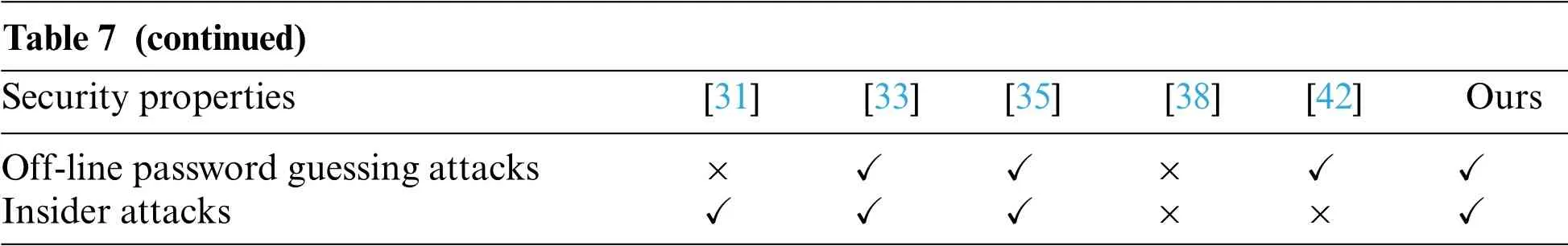
Table 7 (continued)Security properties [31] [33] [35] [38] [42] Ours Off-line password guessing attacks × √ √ × √ √Insider attacks √ √ √ × × √
6.2 Performance Comparison
Here, we compare the performance of these five protocols from two aspects:computional cost and communicational cost.
We adopted a computer with Windows10 operating system,Intel(R)core(TM)i5-8500CPU@3.00 GHz 3.00 G processor, and 8 G memory.The development software we use was IntelliJ idea version 2019.3, which is based on the call of Java pairing library, signature library, and symmetric encryption/decryption function.We ran various operations on the computer 50 times,and then use the average value as the reference time for calculating the computional cost.In addition,we approximate the operation time of the fuzzy extractor to the calculation time of point multiplication, and the computational cost of XOR and join operations is negligible.Based on the results in Table 8,we can drive the comparative results of computational cost in Table 9 and Fig.8(original).The reason why the computational cost of protocols[33]and[35]is very high is that they both use point multiplication,and protocol a also uses symmetric encryption and decryption, which leads to great computational overhead.The reason why the computational cost of our protocol is higher than that of protocols[31,33]and[42]is that we use a fuzzy extractor,which occupy some computational overhead,and they only use one-way hash functions,resulting in slightly higher computational cost.
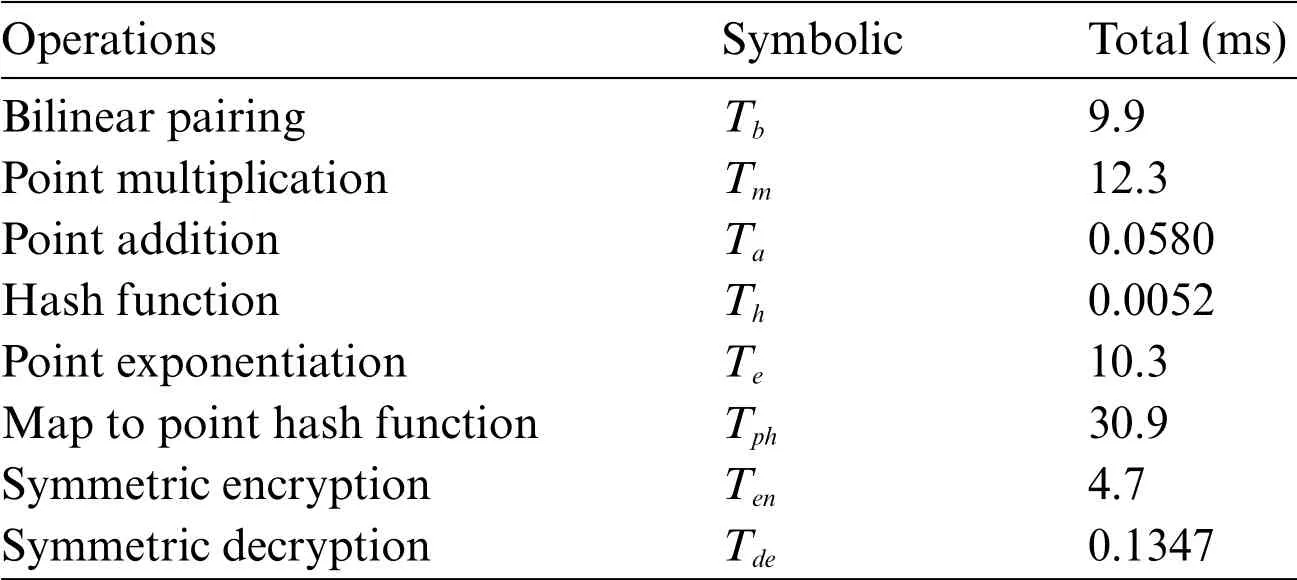
Table 8:The computational cost of complex operations
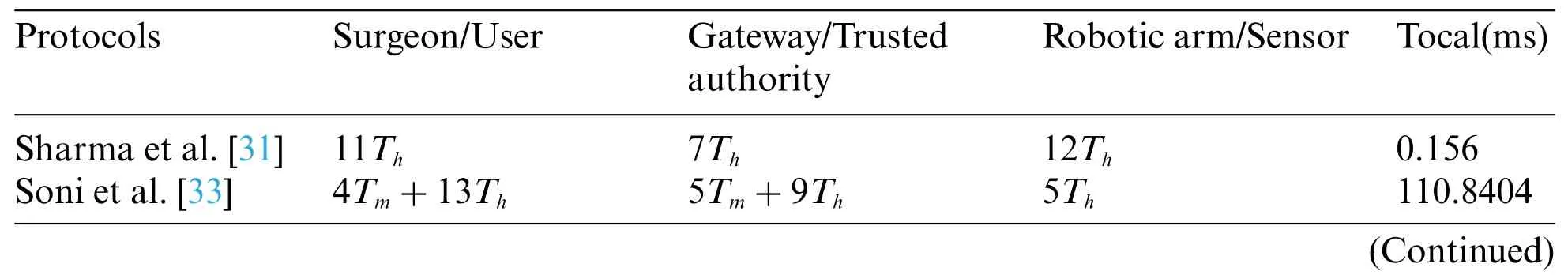
Table 9:Comparative results of computational cost

Table 9 (continued)Protocols Surgeon/User Gateway/Trusted authority Robotic arm/Sensor Tocal(ms)Kaur et al.[35] 4Tm+6Th+2Ten+Tde 6Tm+4Th+2Ten+2Tde 3Tm+2Th+Ten+2Tde 184.1359 Masud et al.[38] 3Th 4Th 2Th 0.048 kamil et al.[42] 8Th 8Th 4Th 0.104 Ours Tm+13Th 19Th 7Th 12.5028
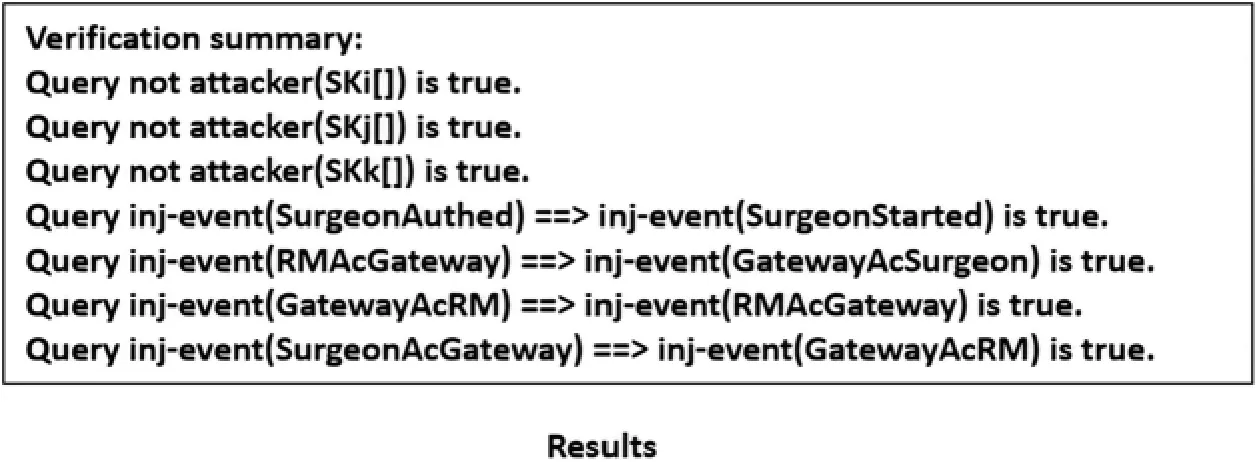
Figure 8:Results
For the communicational cost,we established that the output length of the single hash functionHis 256 bits,Trepresents the timestamp,with a length of 32 bits,IDrepresents the length of the identity and is 256 bits, the length of encryption operationEis 256 bits, the length of groupGis 1024 bits,andsrepresents the string with a length of 160 bits.According to the above definitions,Table 10 and Fig.10 comprehensively show the results.
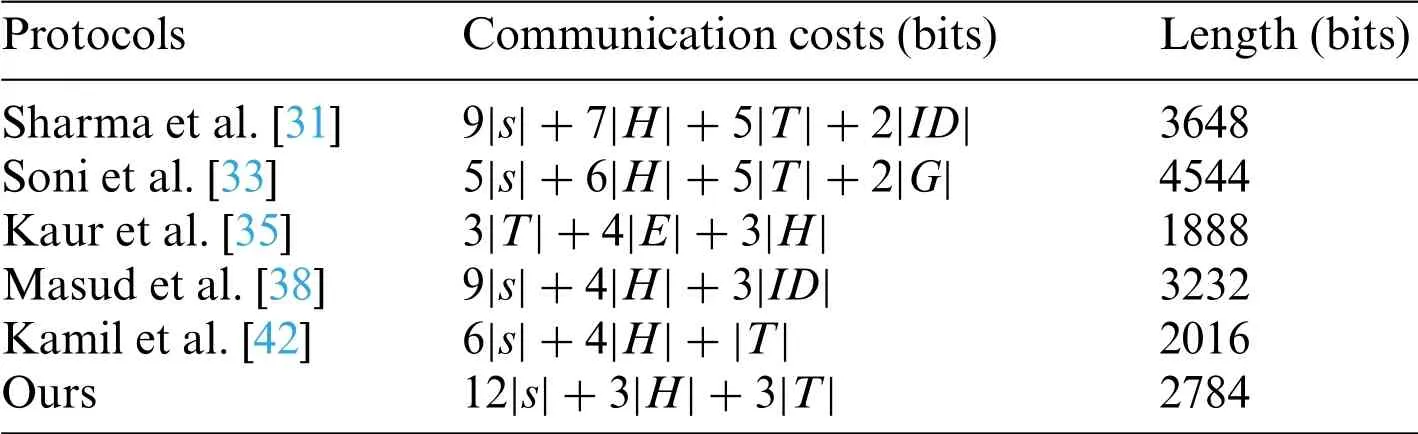
Table 10:Comparative results of communicational cost
To sum up:Table 7 shows the comparison results of security.Table 9 and Fig.9 are the comparison results of computational cost.Table 10 and Fig.10 are the comparison results of communication cost.Although the computing cost of Sharma et al.[31]protocol is lower than ours,its security is not as good as ours, and the communication is also higher than ours; The protocols of Soni et al.[33] is not as good as our protocols in terms of security and performance; Although the protocol of Kaur et al.[35] is more secure and the communication cost is lower than ours, its computing cost is very high;Although the computational cost of Masud et al.[38]protocol is lower than ours,it has security problems and higher communication cost than ours; Although the protocol of Kamil et al.[42] has high performance and is better than ours,its security is worse than ours.
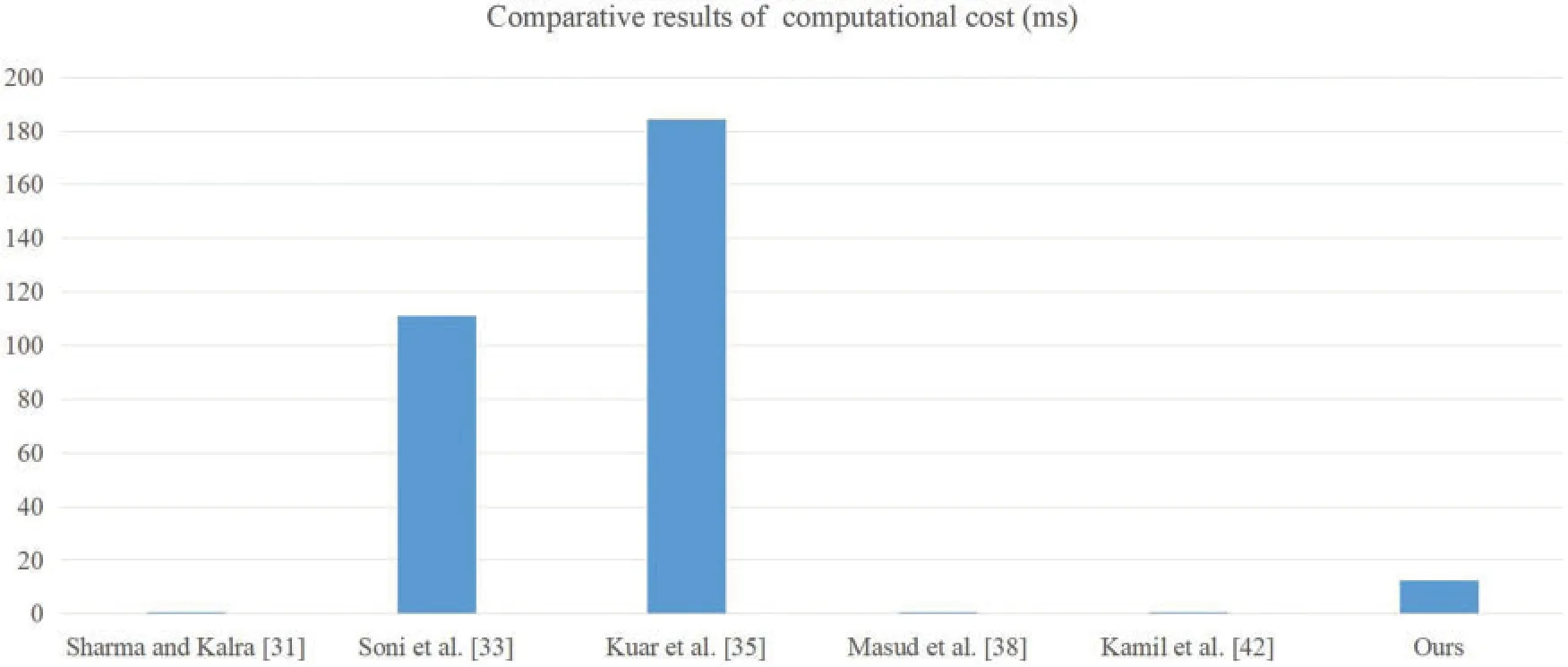
Figure 9:The comparison results of computational cost
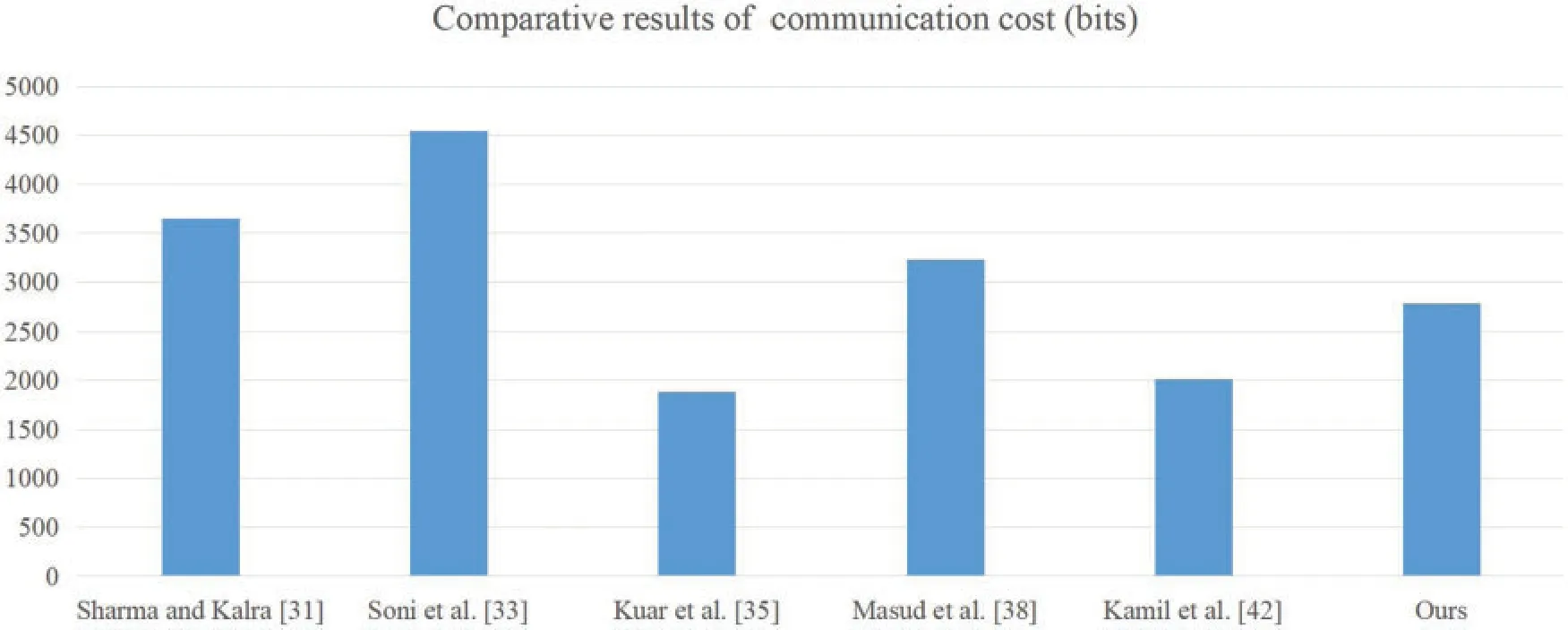
Figure 10:The comparison results of communication cost
7 Conclusion
In this paper,through the cryptanalysis of the protocol proposed by Kamil et al.,we determined that their protocol cannot resist temporary value disclosure attacks and insider attacks.Then, we designed a novel authentication and key agreement protocol for remote surgeries in tactile network environments.We verified the security of our protocol via informal security analysis, and the ROR model and Proverif conducted formal security analysis on our protocol to further validate the security of the protocol.Finally, the performance comparison further indicates that our protocol is more suitable for tactile network environments.Furthermore,we hope that our research results will provide guidance for the development of intelligent medicine.
Funding Statement:The authors received no specific funding for this study.
Conflicts of Interest:The authors declare that they have no conflicts of interest to report regarding the present study.
 Computer Modeling In Engineering&Sciences2023年1期
Computer Modeling In Engineering&Sciences2023年1期
- Computer Modeling In Engineering&Sciences的其它文章
- A Fixed-Point Iterative Method for Discrete Tomography Reconstruction Based on Intelligent Optimization
- A Novel SE-CNN Attention Architecture for sEMG-Based Hand Gesture Recognition
- Analytical Models of Concrete Fatigue:A State-of-the-Art Review
- A Review of the Current Task Offloading Algorithms,Strategies and Approach in Edge Computing Systems
- Machine Learning Techniques for Intrusion Detection Systems in SDN-Recent Advances,Challenges and Future Directions
- Cooperative Angles-Only Relative Navigation Algorithm for Multi-Spacecraft Formation in Close-Range
